 The world of cyber-crime has grown so much in these past few years due to the explosion of growth with respect to the number of internet users the world over. It has not only expanded on the side of normal people but on the side of cyber-criminals who now operate on their own networks, spanning the globe and ready to spread their products, malicious code that first scans the globe for weak points in the security net that we all put up to somewhat give us a sense of security from the ever-growing threat which is actually futile to some extent. [Read more…]
The world of cyber-crime has grown so much in these past few years due to the explosion of growth with respect to the number of internet users the world over. It has not only expanded on the side of normal people but on the side of cyber-criminals who now operate on their own networks, spanning the globe and ready to spread their products, malicious code that first scans the globe for weak points in the security net that we all put up to somewhat give us a sense of security from the ever-growing threat which is actually futile to some extent. [Read more…]
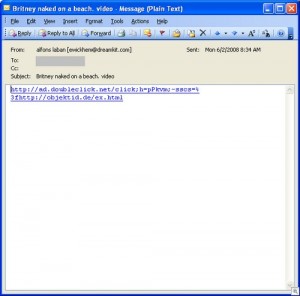
Assigning Limited Email Space and Security

A lot of the viruses and Trojans today find their way into a network or a computer using emails. They come in the form of links or attachments which are always a risk for anyone especially if they don’t have the proper software to screen these files being sent via email. One good way to go about it is to set limits as far as the main email configuration server is concerned. While it may not be able to screen links in emails, attachments of any sort can be minimized.
A good way to provide manual preventive measures is through memorandums and of course lectures that IT personnel can provide to the people in an organization. Newsletters are another option, warning people of virus alerts and how they can make their way into computers.
Spreading in networks starts from one computer. These are a given. So if network and security administrators want to avoid having to address such issues, it would be best to start by safeguarding workstations and orienting people of the threat of such.
Of course, not all people will be listening to you. As far as they are concerned, it is the duty of IT personnel to block them off even before they reach the individual mailboxes. Petty as it may seem, it would be best to use all precautions necessary. While many people will not cooperate, there are measures a good IT person can do and it all starts with research and beefing up security measures through software and policy declarations.
Keep Track of Computer Room Activities

For most companies, the computer room where the company servers containing the delicate data originating from daily transactions is the most important place in the office. So while the people here are trying to figure out ways to safeguard these servers, it would be likewise important to consider external security measures such as placing locks and monitoring the activities with the use of spy cams.
Why is this important? The right question should be geared on how well do you trust you IT personnel. Evaluate their personality and see the extent to which they may betray the company and place operations in jeopardy. This not of course to discredit them but in reality, a lot of people use their knowledge and access as leverage towards being able to command salaries and money-related deals that many of us know as blackmail.
Also, physical intrusion is always a possibility. No matter how secure your area would be, it can be breached at anytime if you do not address the right measure to make it harder for them to gain access to the computer room. In short, the harder it is to get in to you computer room, the better it is. This only means you have prepared on the physical aspect of securing your IT area which is a good approach the sake of safeguarding hardware and data.
Malware is Always a Click Away
One click is all it takes to be infected and for the avid PC user, it would be wise to make sure that you look before you click. Malware issues can come in different forms like:
1. Emails
2. Popups
3. Links via Instant Messaging
In fact, even if you know the person who sent you the link, you cannot entirely rely on your relationship and trust with them as the main reason for clicking on the link. This was done before but today, people have to be aware that there are some accounts that can be easily hacked or even impersonated.
Much of these issues have plagued us through the years. Some have had their share of problems dealing with Malware and Trojans. They are different from viruses but sometimes, they can do more harm compared to the traditional viruses.
Even having anti-virus or anti-spyware protection is not guarantee from being contaminated with them. Remember, a click is all that it takes and all hell will break loose. For most, it is easy to remedy since they can reformat their computer. But think about the files you may lose from the moment you click on these links.
It may be hard to save these files since chances are they have already been infected. With that said, your files and PC are practically good as dead. So the moral of the lesson is, don’t be trigger happy with clicking. You are just raisin the stakes of being infected by doing so.
How To Catch a Worm in a Network
Worms and Trojans can make their way into local intranets fast if you don’t have a good firewall to protect your networking environment. Most of it originates from overlooked files like granting access to the Internet for specified users. But rest assured, unless you document and orient these people on potential risks, chances are the ones to whom you grant access will be the bane of your network security issues.
A worm can multiply fast if not contained immediately. For one, it can affect the whole network. So how do you go about it?
1. Unplug all the computers from the network. Cable disconnection would be a good start. If they are not connected, then there is no place for them to go. Depending on the number of workstations, you may have your work cut out for you. But at least it defeats the need to come and go from one workstation to the other once one is cleaned.
2. Scan the computers manually using a CD. As much as possible use a write-once optical disc. This way, if you find the worm or virus, you have it cornered. There is no place to hide nor go for them.
3. Restart and make a second check. Make sure everything is clean for one workstation. Do this for the rest of the computers that have been potentially affected.
This process requires a lot of patience. But it beats having to turn to the usual formatting and clean everything from scratch. It is indeed demoralizing, but the thing is, you just have to deal with it since better security policies need to be enforced on your end as far as users are concerned.
Implement a Strict IT Policy
It is perhaps the headache of any IT head when it comes to implement policies to have a smooth running network and department. But while the essence of a good security system is evident, it is really the implementation part that is hard to accomplish.
For one, the transition and building of security awareness from various threats that can easily make their way towards an acclaimed secure network is abundant. Manually or transmitted, suspicious files will always find a way especially if you are not that adamant towards making sure that all bases are covered as far as the security of your system and data is concerned.
Many people fail to appreciate that value of the data they have gathered. They fail to appreciate the value of a strict IT policy mainly because all they care about is a workstation to use and opening files (both internal and external) as they please. So if you put all these things together, you can imagine the problems that an IT guy has to work with. But to some, taking the initiative such as passwords and some hardware exclusions has to be made.
If you notice, some drives like the usual floppy drives or even USB ports are either missing or disabled. To make them work, certain permissions and passwords are set for them to be enabled. Only the IT administrator would know these security measures and basic as they may seem, they really help a lot.
This is just a basic but effective way that IT personnel use. There are the usual network policies but for the sake of people who want to making it doubly sure, old and basic practices such as this is perhaps the best way to go.